
LinkedIn Content for Cybersecurity Firms
LinkedIn content that establishes your firm as the security authority that enterprise and mid-market clients turn to first.
Try It FreeSee what Zvario creates
Branded carousels, graphics, and posts — tailored to your message.





Carousels
5-slide branded PDF — ready to post on LinkedIn and social media.
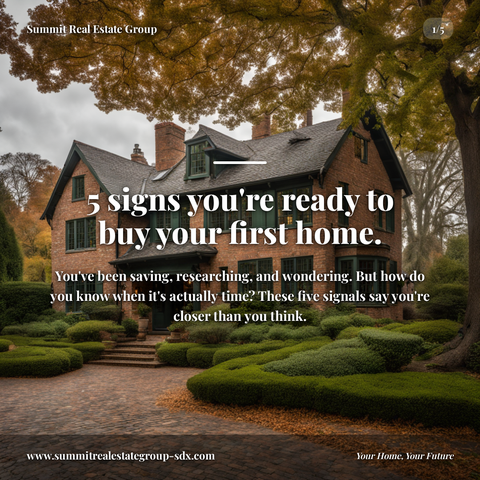
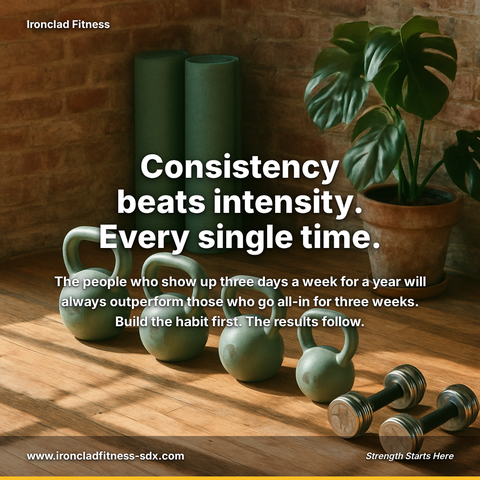
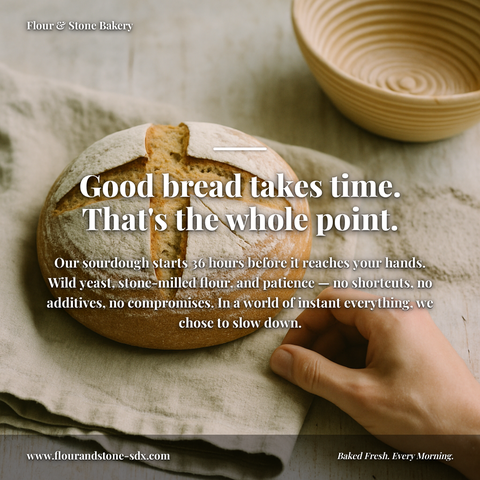
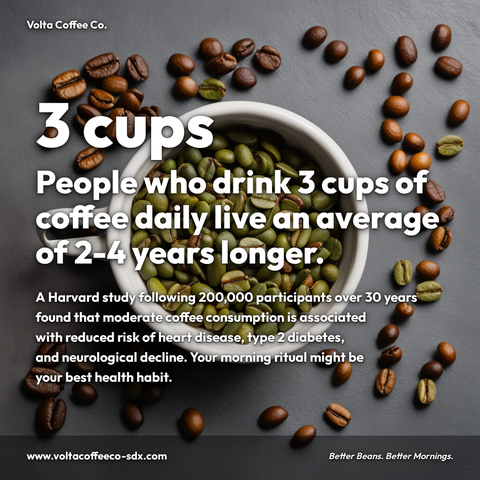
Branded Graphics
Single eye-catching image with your brand colors and message.
Text Posts
Thought leadership copy — ready to paste and publish.
What is Cybersecurity Firms social media content?
Social media content for Cybersecurity Firms refers to LinkedIn posts, carousels, and visual frameworks designed to showcase threat intelligence, risk assessment methodologies, and security architecture expertise to enterprise and mid-market decision-makers. This matters because establishing authority through educational content directly influences client acquisition, builds trust with C-suite prospects, and differentiates your firm in a competitive landscape where buyers research vendors extensively before engagement. LinkedIn carousels generate 3-5x higher engagement than standard image posts, making them ideal for sharing APT threat actor profiles with TTPs and defensive countermeasures, risk quantification frameworks comparing qualitative versus quantitative approaches, or zero-trust architecture implementation roadmaps with phased deployment timelines. Each piece positions your firm as the go-to security authority rather than one option among many. The challenge lies in producing consistent, high-quality content at scale without straining internal resources. Zvario solves this by generating publication-ready cybersecurity social content aligned with your firm's expertise and messaging. Zvario generates this content in under 2 minutes from a single topic, enabling your team to maintain authority presence without the overhead.
Security Buyers Are Building Their Vendor Lists on LinkedIn
CISOs, IT security managers, and compliance officers actively consume LinkedIn content on emerging threats, regulatory changes, and security framework implementation. Cybersecurity firms that publish consistent expert content on LinkedIn are shortlisted when procurement processes open — firms that don't are invisible. The buying committee evaluates vendors not just on capabilities, but on demonstrated thought leadership and understanding of their specific threat landscape.
Threat Intelligence and Compliance Content Commands Attention
Security content that provides genuine intelligence — specific threat actor behavior, regulatory interpretation, framework implementation guidance — consistently outperforms generic security awareness content. LinkedIn audiences in security are sophisticated; they can distinguish between substantive analysis and marketing messaging. Content that demonstrates real expertise in areas like zero-trust architecture, supply chain risk management, or sector-specific compliance requirements earns the engagement that drives inbound pipeline and positions your firm as a trusted advisor.
Establish Credibility Through Methodology-Driven Content
Enterprise buyers need proof that your firm understands their operational challenges. Publishing content around your proprietary assessment methodologies, risk quantification approaches, and remediation frameworks builds credibility without exposing client details. Case study patterns, anonymized lessons learned, and framework comparisons establish your firm as a strategic partner rather than a tool vendor, which directly influences RFP outcomes and contract value.
Build Your Firm's Thought Leadership Pipeline
Individual security practitioners at your firm — architects, incident responders, threat researchers — are your most credible content creators. When your team members publish on emerging threats, advanced persistent threat (APT) attribution, or defensive controls, they build personal authority that reflects on your firm's brand. This distributed approach to thought leadership generates more reach than corporate account posting alone and creates multiple entry points for prospect engagement across different buyer personas and threat focus areas.
Generate Qualified Leads from Security Community Engagement
Consistent content on LinkedIn attracts organic engagement from buyers actively researching solutions. Security practitioners who comment on your posts, share your threat landscape analysis, or ask clarifying questions about your framework recommendations are often early in their procurement cycle. Zvario helps you identify these engaged prospects and nurture them with follow-up content tailored to their expressed interests — whether that's incident response readiness, compliance acceleration, or threat hunting programs.
What you can create for Cybersecurity Firms
- APT threat actor profiling carousels with TTPs, known targets, and defensive countermeasures
- Risk quantification framework posts comparing qualitative vs. quantitative assessment approaches
- Zero-trust architecture implementation roadmap graphics with phased deployment timelines
- Compliance control mapping posts (e.g., NIST CSF to CIS Controls to ISO 27001)
- Incident response playbook templates and breach timeline analysis posts
- Supply chain risk assessment methodology threads explaining vendor third-party risk evaluation
- Security control effectiveness benchmarking posts with industry-specific maturity models
- Regulatory change impact posts on HIPAA/PCI-DSS/SOC 2 updates with implementation guidance
Sample topics to get started
Frequently asked questions
How do we share specific threat intelligence without exposing classified or sensitive client information?
Zvario helps you develop content around threat patterns, TTPs, and defensive controls at the industry level rather than company-specific details. You can discuss attacker behavior, targeting patterns, and your firm's defensive recommendations without requiring client disclosures. This approach demonstrates expertise while protecting client confidentiality — which actually increases trust with prospects evaluating your firm.
Our clients are enterprise-level with long sales cycles. Does LinkedIn drive real pipeline for us?
Yes. Enterprise security buyers — especially CISOs and security directors — are among the most active professional content consumers on LinkedIn. They use the platform to research emerging threats, evaluate vendor approaches, and build shortlists during procurement windows. Consistent, substantive content positions your firm to be discovered at the exact moment they're evaluating solutions. Zvario helps you track which topics and content formats generate the most engagement from your target buyer personas.
How often should our security team be publishing to stay visible to prospects?
Consistency matters more than frequency. Publishing 2-4 pieces per week from your team members (across your firm's accounts) keeps your firm visible in your buyers' feeds without overwhelming your team. Zvario's content planning features help you coordinate across multiple contributors, schedule content for optimal timing, and ensure you're covering the threat and compliance topics your specific buyer segments care about most.
Should we publish on threats and compliance, or also share firm updates and hiring posts?
Lead with expertise content — threat analysis, compliance frameworks, methodology posts — which builds credibility and attracts inbound interest. Mix in thoughtful firm updates and culture posts (selectively) to humanize your brand, but keep your ratio weighted toward substantive security content. Zvario helps you balance content types so your feed establishes authority while building brand affinity with prospects and potential employees.
How does Zvario help us customize content for different security buyer personas (CISO vs. compliance officer vs. security architect)?
Zvario's templating and variant features let you tailor the same core insight for different personas without creating entirely new content. For example, a framework comparison post can be customized to emphasize regulatory requirements for compliance buyers, operational implementation for architects, and strategic risk management for CISOs. This approach maximizes your content reach and relevance while reducing the time your team spends writing variations of the same message.